Download PDF
Download page Interferences / Jamming / Spoofing.
Interferences / Jamming / Spoofing
Accurate satellite-based positioning has become an inherent part of our life in the last decades with increasing accuracy, lower size, and price drop. However, while Global Navigation Satellite Systems (GNSS) deliver incredible performances, the nature of the technology makes it vulnerable to perturbations: it is comparable to the power emitted by a 60W light bulb located more than 20,000 km away from the surface of the earth. This means that the signal received on earth is very "weak," and it is therefore trivial to generate a signal from the surface that will be much stronger than the signal from the satellite.
This happens regularly, both unintentionally (local interferences and RF pollution) and intentionally (intentional interferences or fake signal).
Interferences and Jamming
Unintentional interferences are commonly generated by a variety of devices. Signals generated close to or within the GNSS spectrum may cause an issue. It is, for example, common for USB3.0 devices or some LIDAR sensors to create interferences in the GPS L1 band (1575.42 MHz +/-10 MHz), causing GNSS receivers to fail to provide an accurate position unless proper shielding is added.
Some people or organizations may intentionally create interferences to prevent GNSS receivers from working in a specific area. This is called jamming, the voluntary interference of GNSS signals by transmitting powerful radio frequency signals that overwhelm the weaker GNSS signals.
It is important to note that jamming is not limited to war actions. Many jamming situations are caused by low-cost GPS jammers that are, often illegally, used to prevent a car or a truck position tracking.
Spoofing
Spoofing, on the other hand, involves the creation of counterfeit GNSS signals that fool receivers into calculating false positions and providing inaccurate positioning information.
While jamming is a relatively simple and inexpensive attack, spoofing requires much more advanced equipment and knowledge to be able to carefully mimic the GNSS signals. Note that spoofing is often combined with jamming: it allows the spoofing of only a subset of the GPS signals rather than all the signals at once, making it significantly easier.
GNSS/INS Integration
Our GNSS aided Inertial Navigation Systems implement a three-step approach in the event of interference and/or spoofing:
- Mitigate: our products filter the GNSS signal to maintain a correct GNSS position / velocity for as long as possible.
- Alert: as soon as we detect a potential threat, we alert the integrator to take action (each integrator will react differently to a threat based on the mission profile).
- Circumvent: if a threat cannot be mitigated, we rely on pure inertial navigation to continue outputting position and attitude.
Technologies our Products Use to Mitigate and Alert
To mitigate and alert of jamming or spoofing attempts we rely on advanced algorithms to detect the event and filter the source:
- Multi-constellation and multi-frequency operations: all of our integrated receivers are multi band (either L1/L2 or L1/L2/L5) and support all constellations (GPS, GLONASS, Galileo, Beidou). This increases the resilience to attack which will have a harder time targeting all constellations and especially all frequency bands.
- Interference mitigation: radio emitters such as a Software Defined Radio (SDR) or Personal Privacy Devices (PPD) can easily overpower the GNSS signals and cause a blackout. Our navigation systems incorporate interference mitigation technologies that attenuate the effects of jamming devices by applying a specific filtering as needed.
- Sophisticated spoofing algorithms are also integrated to detect potential spoofing attempts.
- Receiver Autonomous Integrity Monitoring (RAIM) algorithms are embedded to identify faulty GNSS signals that could be caused by intentional spoofing attempts (or by multipath).
- Finally, inertial navigation system integration enable dead reckoning for a certain time during GNSS outages. Using aiding sensors like odometry can greatly extend the dead reckoning period.
Which feature on which products?
To find out which features are included in each product, please refer to the functional specifications or contact our support team for assistance.
Message Authentication with OSNMA
On top of these Radio Frequency analysis technologies, some of our products use Galileo’s Open Service Navigation Message Authentication (OSNMA) to authenticate the sender of the message as described below.
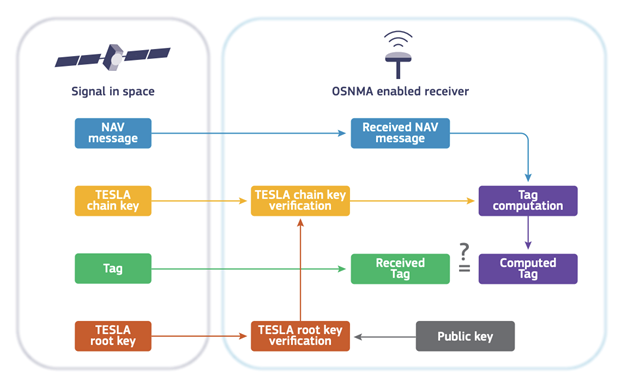
All the signals sent by Galileo satellites include a key that is authenticated using asymmetric cryptography techniques. At the receiver end, the public key is used to verify that the signature is valid and to confirm that the sender of the signal is the expected Galileo satellite.
This makes it almost impossible to spoof Galileo signals.
Our current products with embedded GNSS are OSNMA ready. Once the testing phase is completed, the feature will be enabled with a Firmware update.